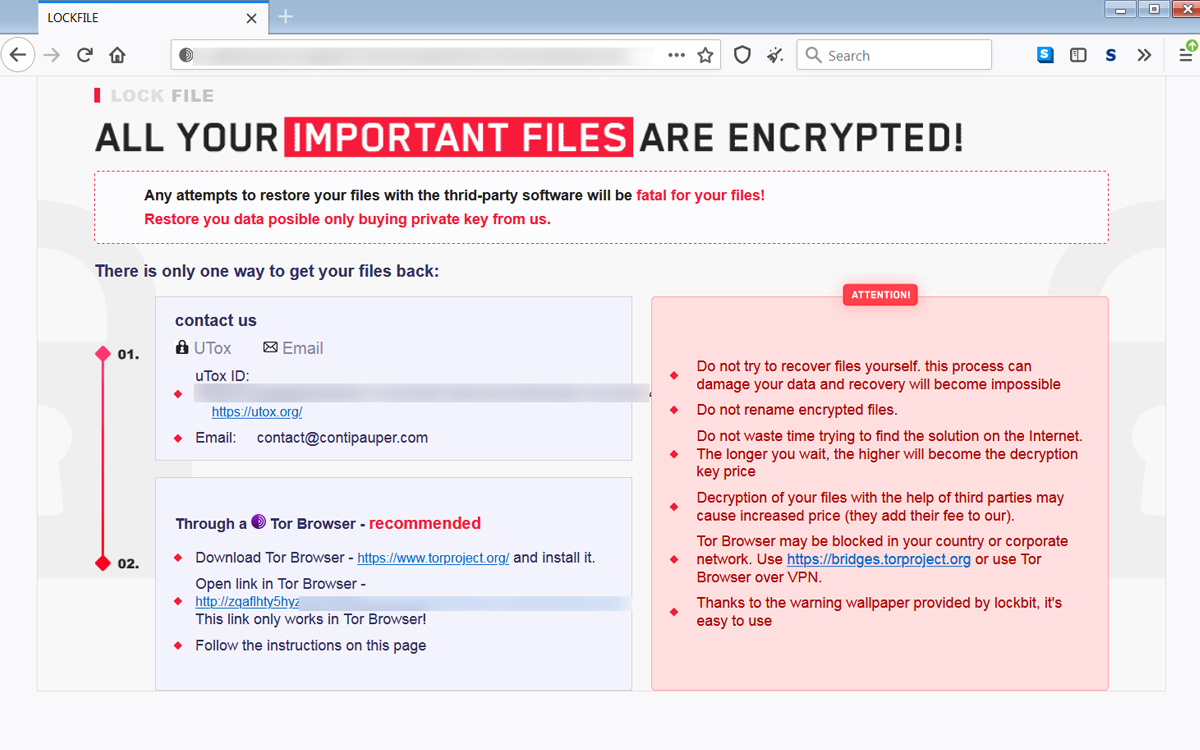
A new ransomware family called LockFile has started targeting Microsoft Exchange servers via ProxyShell and PetitPotam.
Security researchers have discovered a new ransomware family called LockFile that appears to have been used to attack Microsoft Exchange servers in the US and Asia since at least July 20.
Symantec says that when it revealed LockFile on Aug. 20, it found evidence of the ransomware targeting at least 10 organizations over the course of a single month. The security company says LockFile’s operators used an attack called PetitPotam, which targets a domain controller to gain control over an entire network, but it didn’t know how the attackers gained access to the servers.
DoublePulsar’s Kevin Beaumont does. He reports that his personal honeypot project—an intentionally exposed server that can be used to learn more about hacking attempts—was targeted by LockFile’s operators on Aug. 13 and Aug. 16. Those attacks revealed that LockFile was exploiting a series of vulnerabilities in Microsoft Exchange known collectively as ProxyShell.
ProxyShell is one of three collections of vulnerabilities affecting Microsoft Exchange discovered, exploited, and disclosed by Devcore principal security researcher Orange Tsai. The attack surfaces were shown off at the Pwn2Own hacking competition in April, and Tsai shared more information about them during a talk at the Black Hat 2021 conference on Aug. 5 as well.
Microsoft patched these vulnerabilities in May, but BleepingComputer reports that researchers and hackers alike have been able to recreate the exploit, which is now being used to enable the LockFile attacks. The ransomware’s operators can also target Exchange servers that haven’t received the latest updates and therefore remain vulnerable to the original ProxyShell attacks.
Beaumont says there are still “hundreds of directly exploitable, internet facing systems with *.gov SSL certificate hostnames” in the US as of Aug. 21 and cited TechTarget’s report that “tens of thousands of Exchange servers are still vulnerable to ProxyLogon and ProxyShell.” Some of those are likely to be honeypots, according to the report, but most probably aren’t.